Table of Contents
ToggleSecurity is a major concern for all businesses in today’s rapidly evolving digital landscape. With the constant advancements in technology, the threat landscape continues to grow and evolve. Business leaders and security professionals bear the responsibility of safeguarding sensitive information, intellectual property, and customer data from potential incidents and cyber threats. To effectively address these challenges, relying on the latest security developments and best practices is essential. A 2021 survey highlighted that nearly 50 percent of respondents rely on the NIST Cyber Security Framework (CSF) standard to plan their control systems, underscoring the importance of standardized approaches in cybersecurity efforts. Ongoing education and the implementation of proactive strategies are imperative for establishing resilient security frameworks. These frameworks not only provide a solid foundation for defense but also demonstrate adaptability to the constantly changing nature of cyber threats. By being well-informed, businesses can effectively reduce risks, safeguard critical assets, and create a robust defense mechanism against the evolving security challenges. As companies embrace the latest security measures and continuously educate their teams, they are positioned to navigate the intricate cybersecurity landscape with confidence and resilience.
What is the National Institute of Standards and Technology (NIST)?
The National Institute of Standards and Technology (NIST) is a non-regulatory federal agency under the United States Department of Commerce. With a primary objective of fostering innovation and enhancing industrial competitiveness, NIST focuses on advancing measurement science, standards, and technology to enhance economic security and enhance the overall quality of life. One of the ways NIST works towards its mission is by providing the NIST Cybersecurity Framework, which serves as a valuable resource for individuals seeking to demonstrate cybersecurity practices.
What is the NIST Cybersecurity Framework?
The NIST Cybersecurity Framework (CSF) is a set of guidelines, best practices, and standards designed to help organizations manage and improve their cybersecurity risk management processes. It was established in 2013 to provide guidance on how to enhance the cybersecurity of critical infrastructure. The NIST Framework offers businesses a strategic roadmap and best practices to allocate resources effectively for comprehensive protection. By following this voluntary framework, businesses can improve their cybersecurity strategy, which helps them save a considerable amount of time and money to safeguard their digital assets.
The NIST framework is particularly advantageous for smaller or less-regulated entities seeking to increase awareness and enhance security measures. Implementing the NIST Cybersecurity Framework empowers smaller businesses to prioritize security and navigate potential risks efficiently. On the other hand, larger enterprises may find its value diminished due to existing comprehensive security programs. Adapting the NIST framework can be a strategic move for startups and less-regulated sectors aiming to fortify their cybersecurity posture and cultivate a heightened sense of security awareness.
Three Key Elements of the NIST Cybersecurity Framework (CSF):
The NIST Cybersecurity Framework provides a guide for businesses striving to enhance their cybersecurity capabilities. At its core, the framework is built upon two essential components: Core Functions, and Framework Implementation Tiers. Let’s take a deeper look into each component:
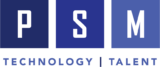
- Core Functions: Within the core functions section of the framework, it outlines five key functions – Identify, Protect, Detect, Respond, and Recover. These functions are the key areas that businesses need to focus on to manage and improve their cybersecurity posture.
- Identify: Recognize and prioritize assets, risks, and vulnerabilities.
- Under this core function establish and distribute a company cybersecurity policy encompassing roles and responsibilities for employees, vendors, and any individuals with access to sensitive data.
- Protect: Use precautions to safeguard the provision of critical infrastructure services.
- In this core function, ensure that security software is utilized to safeguard data, control access to your network and devices, and provide cybersecurity training for everyone using computers and devices within the network.
- Detect: Develop and employ monitoring strategies to identify cybersecurity events.
- Within this core function, investigate any unusual activities on your network or by your staff and regularly check for unauthorized individuals or connections.
- Respond: Develop and implement an effective incident response (IR) plan to mitigate the impact of a cybersecurity incident.
- In this core function, establish a plan for notifying customers, employees, and other individuals whose data may be at risk. Maintain business operations and update your cybersecurity policy and incident response based on lessons learned.
- Recover: Begin activities to restore and resume critical infrastructure services.
- In this core function, focus on repairing and restoring damaged equipment and network components. Keep employees and customers informed about your response and recovery activities.
- Identify: Recognize and prioritize assets, risks, and vulnerabilities.
2. Categories and Subcategories: Within each core function, the framework provides more detailed information in which are located in categories and subcategories that help organizations implement specific cybersecurity practices.
- Identify: Within this function, there are six categories which include asset management, business environment, governance, risk assessment, risk management strategy and supply chain risk management.
- Protect: Under this function, there are six categories which encompass identity management and access control, awareness and training, data security, information protection processes & procedures, maintenance, and protective technology.
- Detect: This function encompasses three categories: anomalies and events, security continuous monitoring, and detection response.
- Respond: Within this function, there are five categories which include response planning, communications, analysis, mitigation, and improvements.
- Recover: This function encompasses three categories: recovery planning, improvements, and communications.
Each category and subcategory within the framework provides a structured approach for organizations to bolster their cybersecurity posture and effectively respond to threats and incidents.
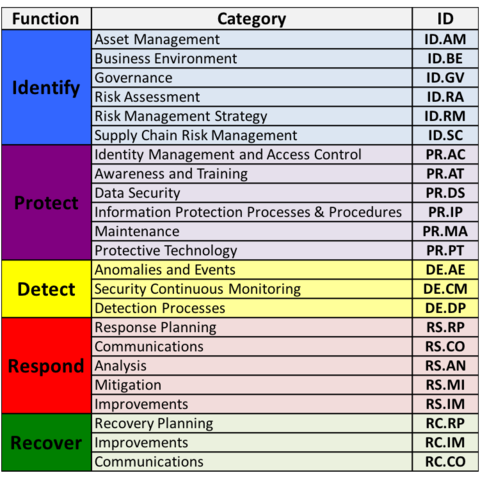
3. Framework Implementation Tiers: This component assists businesses in determining the maturity of their cybersecurity risk management processes. There are four tiers – Partial, Risk Informed, Repeatable, and Adaptive. Each tier represents a different level of cybersecurity maturity.
- Partial: Companies at this tier have an ad-hoc approach to cybersecurity risk management. There may be a lack of awareness of cybersecurity risks, and actions are taken on a case-by-case basis.
- Risk Informed: At this tier, businesses have a more structured approach to managing cybersecurity risks. They begin to establish a formalized risk management process and have a basic understanding of cybersecurity risks.
- Repeatable: Organizations at this tier have established a formalized and repeatable cybersecurity risk management process. The process is consistently applied across the organization, and there is an increased awareness of cybersecurity risks. The organization actively manages and measures its cybersecurity practices.
- Adaptive: This is the highest tier, where organizations have a dynamic and adaptive approach to cybersecurity risk management. They continuously monitor and adjust their cybersecurity practices based on changes in the threat landscape, business processes, and technologies. The organization’s cybersecurity practices are fully integrated into its overall risk management and business strategy.
These tiers provide a way for businesses to assess their current level of cybersecurity maturity and to set goals for improvement based on the Framework’s guidance. The goal is for organizations to progress towards a higher level as they enhance their cybersecurity skills and resilience.
Enhance Your Cybersecurity Defenses: Unveiling the Power of PSM Partners in Safeguarding Your Business
PSM Partners offers proactive Incident Response planning and corrective services in case of a security incident. Serving the Chicago, IL region and equipped with nationwide capabilities, we guarantee comprehensive coverage for our clients, irrespective of their location. Our clients rely on us to provide proficient advisory services for cyber and risk management, conduct cyber readiness assessments, and promptly address any security incident. Recognizing the sensitivity and immediacy of these situations, we have established a tested response protocol that addresses not only the technical aspects but also the business requirements. To learn more about PSM’s Cybersecurity and Incident Response services, Contact us today.
Related Insights
2026 Technology Priorities for Financial Services CIOs & CTOs
Executive Summary As financial services firms move past the experimentation...
Read MoreNonprofit 2026 IT Trends: From AI Adoption to Cyber Resilience
Nonprofits in 2026 are operating in a new environment where...
Read MoreWhat are LOLBins: The Growing Threat
Cybercriminals are becoming increasingly clever at turning everyday tools into...
Read MoreUpcoming Cybersecurity Events in 2026
As technology continues to evolve at a rapid pace, staying...
Read MoreAbout the Author

Taylor Friend
I'm a goal-oriented Strategic Alliance Manager who is enthusiastic about building and nurturing collaborative relationships that drive business success. My commitment lies in establishing, overseeing, and expanding partnerships that generate greater business opportunities and foster revenue growth for all stakeholders.