Table of Contents
ToggleWhat is MFA?
You may already be familiar with Multi-Factor Authentication, or MFA for short. It is also known as Two-Factor Authentication or 2FA. Organizations everywhere are enforcing MFA in Microsoft 365 to bolster their security against an ever-expanding threat of hackers and data thieves looking to gain access into your organizations environment. Hackers may try and get access for a variety of reasons, all of which are nefarious.
In a nutshell, Multi-factor authentication is a multi-step process for verifying your identity. When enforced in M365/Azure or other systems, you verify your identity by presenting two or more pieces of evidence that you are indeed who you say you are. This evidence is something you know (password or PIN), something you have (smartphone app verification, one-time passcode, or a USB key), or something you are (fingerprint or facial recognition).

Figure 1: How it works: Azure AD Multi-Factor Authentication | Microsoft Docs
Having MFA is necessary in today’s world, where security is an arms race between the good and the bad guys. However, the purpose of this article is to educate on why MFA is no longer enough to secure data in Microsoft 365 and why organizations should think about a more comprehensive approach to security and how we use MFA.
What most get wrong about MFA
There is a common argument in the industry that MFA, on its own, is enough to prevent 99.9% of attacks related to credential compromise. However, by modern security standards, MFA is just the beginning and must be employed strategically alongside other tools available.
If a user’s password is leaked or stolen, we can rest easy knowing that a bad actor must still get past the MFA challenge to access any M365 resources, right? Well, not exactly. As we mentioned, MFA by itself is just one security control. Methods exist to bypass even the most secure forms of MFA through a combination of social engineering and technical attack vectors. With that being said, this brings us back to MFA being a piece of a larger puzzle, not the entire security puzzle.
Now that we have established that MFA is a critical control for securing M365 and Azure resources, MFA is not intended to be the sole control for security. MFA is an essential security tool but should be used in combination with a larger, more layered approach to securing access to data in your Microsoft 365 tenant. It is part of Microsoft’s Security Defaults on any newly created Microsoft 365 tenant. Today, MFA is considered the bare minimum requirement as a best practice.
The typical MFA Implementation and the drawbacks
In PSM Partners’ previous experience, we typically see organizations only enforcing MFA on new device sign-in’s and only on intervals of 60 or 90 days. The example above, is usually a hastily implemented solution to satisfy a cybersecurity insurance requirement or a response to a security event. Furthermore, organizations with poor MFA practices will implement insecure forms of MFA authentication, such as, one-time codes sent to the user’s cell phone via SMS or a phone call to confirm the user’s identity. Although, the most secure option is using the Microsoft Authenticator app for push notifications or one-time passcodes (OTP). Companies that finally implement the Microsoft Authenticator app for MFA is usually born out of compromise and or a desire to balance or favor convenience over security.
It is easy to recognize the drawbacks of this type of implementation. For starters, it’s widely known that SMS is not encrypted, vulnerable to interception, and easily lost in a SIM swap attack (FBI: Criminals escalating SIM swap attacks to steal millions of dollars | TechRepublic). Additionally, users are inundated with MFA challenges when accessing an organization’s Microsoft 365 resource for a variety of reasons, leading to autopilot-like action when receiving MFA prompts. Unless specified, there are no controls in place to govern MFA attempts and lockout periods. We have seen that many administrators are simply not aware of these options.
Other ways bad actors can get around MFA
Bad actors are always finding ways of defeating or working around MFA. Security is a cat and mouse game. Enter MFA bombing, a method that’s been known in the security circles and has become more infamous in recent months (Lapsus$ and SolarWinds hackers both use the same old trick to bypass MFA | Ars Technica). MFA bombing is the practice of overwhelming a user with MFA prompts until they accept/approve them. However, MFA bombing is not always an overwhelming prompts attack. It may be conducted more stealthily like presenting an MFA prompt to the user once or twice a day, to sneak past the user’s suspicion. In many cases, users may approve the prompt without giving it a second thought.
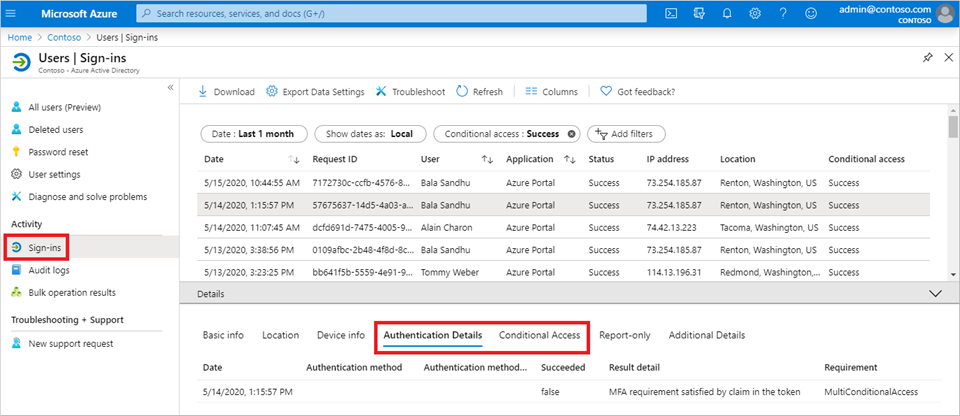
Figure 2: Use the sign-ins report to review Azure AD Multi-Factor Authentication events | Microsoft Docs
Consent Phishing aka OAuth Phishing is an attack vector where a bad actor sends a carefully crafted email message asking the user for access to data (Microsoft warns of increasing OAuth Office 365 phishing attacks | Bleeping Computer). The user approves permission for access through a familiar Microsoft 365 interface, while already signed into Microsoft 365. The attacker is then able to access the user’s data and account, while simultaneously gaining the ability for themselves to enroll a device or another form of MFA as the phished user.
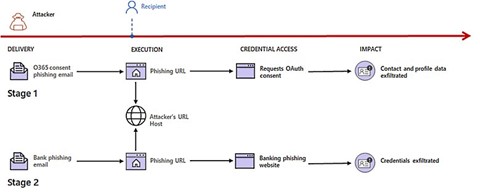
Figure 3: OAuth phishing attack flow | Bleeping Computer
Another method worth mentioning is EvilGinx2. This method is a type of man-in-the-middle attack in which the bad actor tricks the user into visiting a site that looks exactly like their normal Microsoft 365 login. Then, as the user logs in and completes the MFA challenge, the fake site retransmits the user’s login information to a real M365 login page, and the bad actor captures the authentication token in the process. The user logs in to M365 but is none the wiser. The bad actor is now able to replay the token and access M365 as the user.
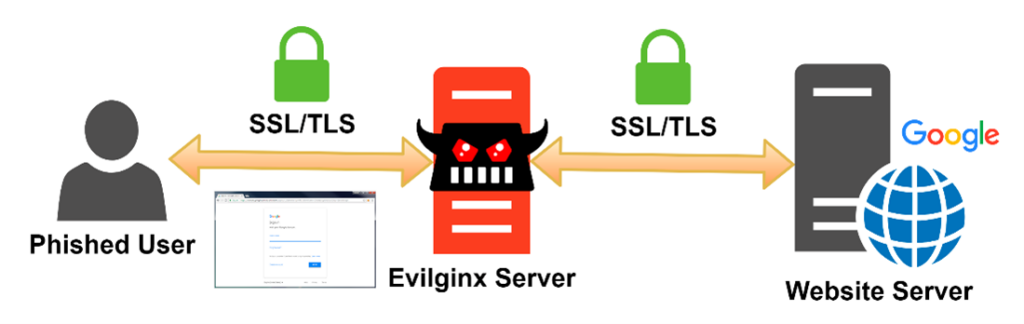
Figure 4: EvilGinx in action | BREAKDEV
What is the solution?
As you can see, having just plain-vanilla MFA in place can lead to a false sense of security. There is a multitude of ways that bad actors can use existing known vulnerabilities and misconfigurations to gain access. Earlier in this article, we mentioned that MFA is a piece of the puzzle and requires a comprehensive approach. While each organization’s threat model is different and may require different mitigations, we always want to start with the fundamentals.
Let us start with education. This is not the most popular topic, but it is paramount. Organizations must continually educate their employees to not only use the technology available to them efficiently and securely but also to spot threats and report them at once. All the technology in the world does not secure against a well-planned social engineering attack. Consider using a cybersecurity education platform to educate and evaluate end-users on a semi-annual basis.

Figure 5: KnowBe4 Security Awareness Training | KnowBe4
If your organization still uses SMS or Phone calls for MFA challenges, consider reducing or dropping their use in favor of the Microsoft Authenticator app (Push Notifications, OTP tokens, or Passwordless authentication methods). Microsoft offers the following comparison chart as part of their MFA Deployment Guide. If you have the option, FIDO2 Security Keys such as the Yubico YubiKey integrate well with Microsoft 365 and provide a top-of-the-range solution for MFA.
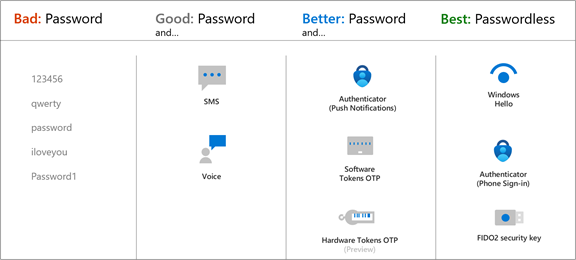
Figure 6: Choose authentication methods for MFA | Microsoft Docs
If your organization is still using legacy per-user MFA, consider using Azure MFA with Conditional Access policies to apply granular controls for when users should be prompted for MFA. Conditional Access is a feature of the Azure AD Premium P1 license and is included in the Business Premium, M365 E3, and M365 E5 licensing tiers, as well as the Enterprise Mobility + Security (EMS) suite. Conditional Access, when properly implemented, allows for a variety of options to confirm user sign-ins more smartly rather than inundating the user with an MFA prompt for every new sign-in attempt. We recommend the Business Premium license for all businesses under 300 seats so that organizations may take advantage of Conditional Access and other features.
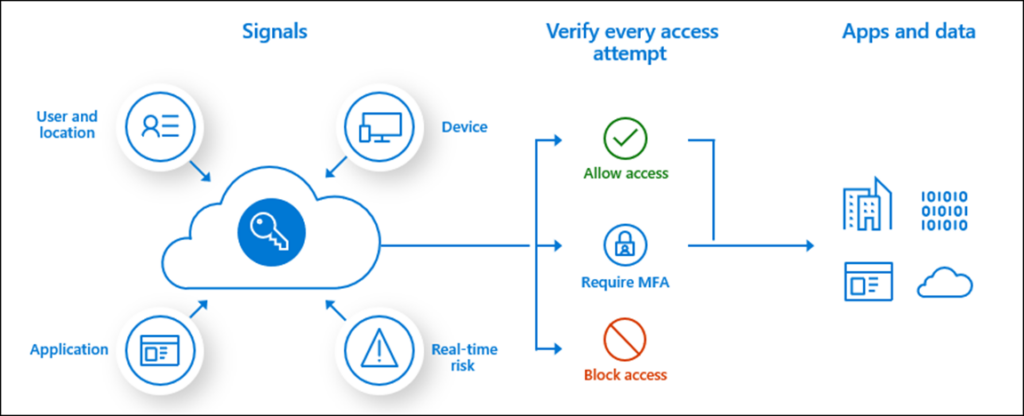
Figure 7: Plan Conditional Access policies | Microsoft Docs
For organizations that have yet to embark on the device management journey, consider deploying Microsoft Endpoint Management (Intune) Mobile Device Management (MDM), and Mobile Application Management (MAM) in your organization. Intune is included in the Business Premium, M365 E3, and M365 E5 licensing tiers, as well as the Enterprise Mobility + Security (EMS) suite. The solution offers multiple options for getting your devices enrolled as organization-owned and BYO devices. Once enrolled and configured, administrators may use Conditional Access to allow or block devices based on device compliance and risk status. Therefore, providing another level of control without inundating users with MFA prompts unless necessary. Mobile devices may be secured through MAM as a least-intrusive method for securing access to organizational data. For organizations that use Group Policy, SCCM, or other device management solutions, Intune offers diverse options to co-manage or replace the incumbent solution with a modern approach.
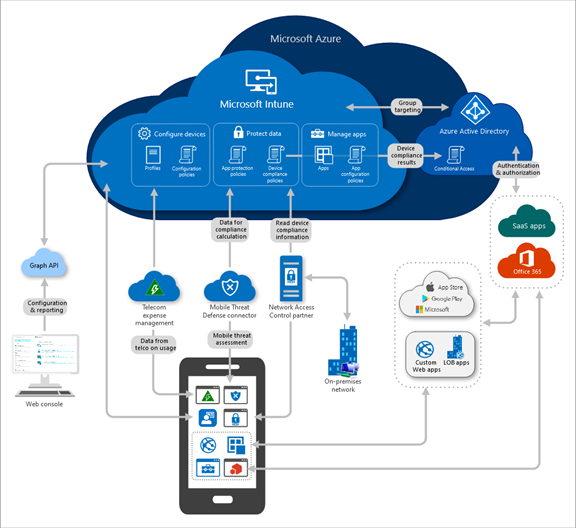
Figure 8: Microsoft Intune is an MDM and MAM provider for your devices | Microsoft Docs
For organizations that leverage Azure AD Premium P2, M365 E5, or the Enterprise Mobility + Security E5 licensing consider implementing Azure Identity Protection and Risk-based Conditional Access policies. Azure Identity Protection is a set of tools that enables organizations to automate the detection and response to user risk or risky sign-ins. Microsoft’s machine learning and heuristic systems evaluate risk scores for over 18 billion login attempts each day. Microsoft checks for leaked credentials that may appear on the dark web and alert the administrator if a user is considered a risk. Additionally, sign-in attempts are scrutinized for risks like anonymous IP addresses, atypical travel, malware-linked IPs, etc. Risk confidence is measured as low, medium, or high. The automated response may require the user to complete an MFA challenge, perform a self-service password change, or block the user’s access until an administrator can review the situation.
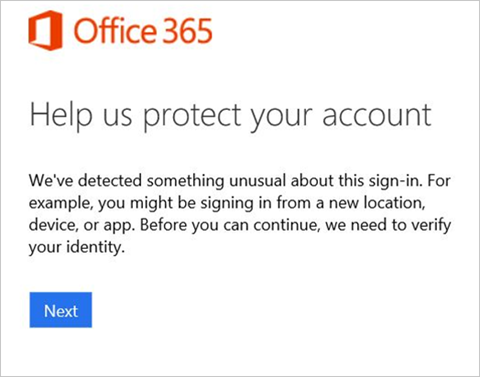
Figure 9: The user is informed that something unusual was detected about their sign-in | Microsoft Docs
How we can help you
There are many more ways that we can use to secure organization data, users, and devices. However, that is outside the scope of this article. We hope that this content provides you with ideas on how to take your MFA implementation to the next level by using what is available to you through your Microsoft 365 tenant.
PSM Partners is a Microsoft Gold Partner technology consulting firm with a focus on client requirements, transparency, and agnostic solutions. Leverage our approach to strengthen your technologies and execute your IT initiatives. Delivered by a team of highly skilled and expertly trained engineers, PSM Partners has helped countless customers implement MFA and is committed to helping your business choose and execute the perfect MFA strategy. Contact us today to get started!
Related Insights
2026 Technology Priorities for Financial Services CIOs & CTOs
Executive Summary As financial services firms move past the experimentation...
Read MoreNonprofit 2026 IT Trends: From AI Adoption to Cyber Resilience
Nonprofits in 2026 are operating in a new environment where...
Read MoreWhat are LOLBins: The Growing Threat
Cybercriminals are becoming increasingly clever at turning everyday tools into...
Read MoreUpcoming Cybersecurity Events in 2026
As technology continues to evolve at a rapid pace, staying...
Read MoreAbout the Author
Ilya Gofman
Passionate and accomplished Information Technology expert with a track record of 17+ years in designing, implementing, and maintaining innovative networks and technologies across various industries. Offers invaluable advice to clients, creates innovative solution architectures, and ensures that technology strategies align seamlessly with business objectives. Recognized as a Microsoft 365 Certified Enterprise Administrator Expert.